The Essential Guide To Implementing AI Cybersecurity Strategies
AI Cybersecurity has been an integral component of most enterprises and helped them scale their operations. This enables companies to conduct real-time network monitoring with intelligent algorithms that can identify and preempt malware from hitting your system before any significant damage occurs.
AI Cybersecurity strategies with ai are no longer an elective for organizations wishing to protect their intellectual property and customer trust. Individual attacks are learned from these systems to produce a Protect, which is a constantly moving line that protects the digital landscape against even the most certain.
Building Secure Frameworks With Neural Network Defense Systems
With the recent trend of digitalization, modern companies have started to put network defense strategies as their priority and continue to stay ahead in this fast-paced market. Through intelligent monitoring tools, administrators can identify unusual activity on their servers and immediately shut off suspect traffic without any manual human input.
Data protection must be constantly active, 24 hours a day, and for that we need an effective network defense infrastructure. This 1-2 punch keeps your primary digital assets safe from the intruders who constantly seek out small gaps in your online perimeter & firewalls.
- Reliable encryption tools protect sensitive communications between your office and remote employees.
- Smart firewalls filter out malicious traffic based on real-time global threat intelligence.
- Regular system updates ensure that your defense tools can recognize the newest vulnerabilities.
- Automated reporting helps your IT team understand the nature of every blocked attack.
- Centralized dashboards provide a clear view of your entire organization's current security status.

Implementing Zero Trust Architecture Within Modern AI Environments
No user or device is trusted, zero trust architecture means no default trust, regardless of whether the cloud-based businesses are located on-premises, at the edge or in any external environment. This strict verification process mandates the identity of every entity to be validated before a sensitive part of your internal network is accessible.
A modern zero trust architecture model minimizes the lateral movement risk of hackers that have penetrated your outer perimeter. By breaking their data up, encrypting it and sending it to different places on the internet, they create uni-directional layers of protection that ensure your most valuable secrets never see the light of day.
In an enterprise-level zero trust architecture environment, all access requests are repeatedly verified and monitored. This level of granularity delivers a powerful enhancement to your security profile and helps ensure compliance with international data protection legislation.
Enhancing Corporate Safety Through Predictive Risk Analytics Tools
Modern businesses leverage risk analytics to identify the possible coming threat within their neural network, which has been proven as an effective way of mitigating such threats. This positive attitude enables managers to patch holes in their software that would, otherwise, be used by criminals.
Smart companies use risk analytics to help them prioritize how they spend their security budget and tackle the most dangerous vulnerabilities first. This data-driven approach works to ensure that each dollar spent on defense offers the greatest possible value across the entire worldwide company.
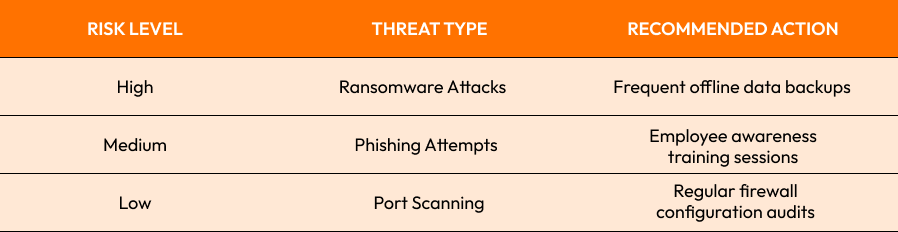
Predictive tools transform how we view safety by turning raw data into actionable intelligence that secures our collective future against the unknown digital world.

Managing Ethics And Cloud Security Protocols For Businesses
For any business with precious customer data that they keep in the cloud, it is crucial to have a tight security protocol. These are providing your technical team with a proper set of guidelines to follow to ensure that all servers are patched so there is no compromise visible.
Established and updated security protocol should be checked at least quarterly to adapt to new trends. This practice ensures your team stays sharp and your digital walls are sufficiently fortified to fend off even the most sophisticated attacks.
- Secure login procedures prevent unauthorized users from accessing your sensitive administrative cloud panels.
- Data encryption at rest ensures that stolen files remain unreadable to any intruders.
- Regular backup schedules provide a safety net in case of a system failure.
- Third-party audits verify that your cloud provider is following the highest security standards.
- Incident response plans help your team react quickly and calmly during a crisis.

Safeguarding Corporate Assets With Intelligent Identity Access Management
Access management tools offer a single point for managing who can view your most critical business documents. By giving every employee a role in the organization, you ensure that people only have access to the data they need to do their day-to-day work.
Smart access management systems use biometric data and multi-factor authentication to ensure the identity of every user. This dramatically reduces the risk that a compromised password triggers a major and very costly corporate data breach.
In addition to granting permissions, effective and modern access management policies include the immediate revocation of permissions for those employees who have left the company as well. It keeps your internal environment clean and prevents ex-employees from having access to these private digital infrastructures.
Conclusion
Ensuring a secure digital landscape is no simple task; it is a delicate balance of cutting-edge technology and the expertise to utilize it correctly. These are steps you can take now, to safeguard your company and provide continuity of operations well into the future.
The next wave of business innovation will be founded on AI cybersecurity. Those organizations that embrace these tools now will be far better equipped to tackle the complex challenges of an increasingly interconnected and digital world.
Ready to secure your business? Contact us to start your journey.
Start Your Expert Consultation
Please write your name and contact information below. We will respond as soon as possible.







